Evading Sysmon DNS Monitoring
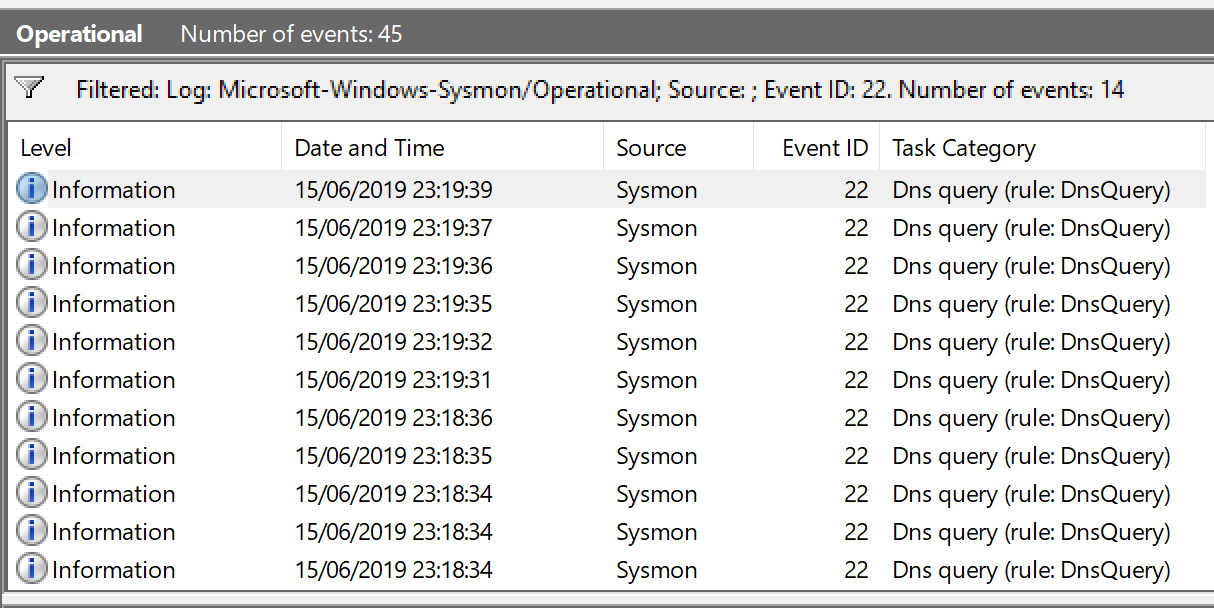
In a recent update to Sysmon, a new feature was introduced allowing the ability to log DNS events. While this gives an excellent datapoint for defenders (shout out to the SysInternals team for continuing to provide and support these awesome tools for free), for us as attackers, this means that should our implant or payloads attempt to communicate via DNS, BlueTeam have a potential way to pick up on indicators which could lead to de
Read More »