Kerberos AD Attacks - Kerberoasting
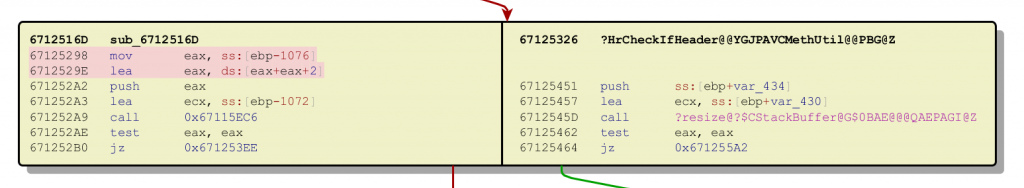
Recently I've been trying to make sure that my redteam knowledge is up to date, exploring many of the advancements in Active Directory Kerberos attacks... and there have been quite a few! I finally found some free time this week to roll up my sleeves and dig into the internals of some of these attacks, and hopefully document them for other people to learn. This post is the first in a series aimed at explaining what is happening under the hood when you execute your favourite Powerview or Mimikat
Read More »