Moving jobs and exploiting flash (CVE-2018-4878)
Recently I joined the MDSec team after seeing many of the cool things that they had contributed to the community, and to hopefully pick up some of their awesome skills.
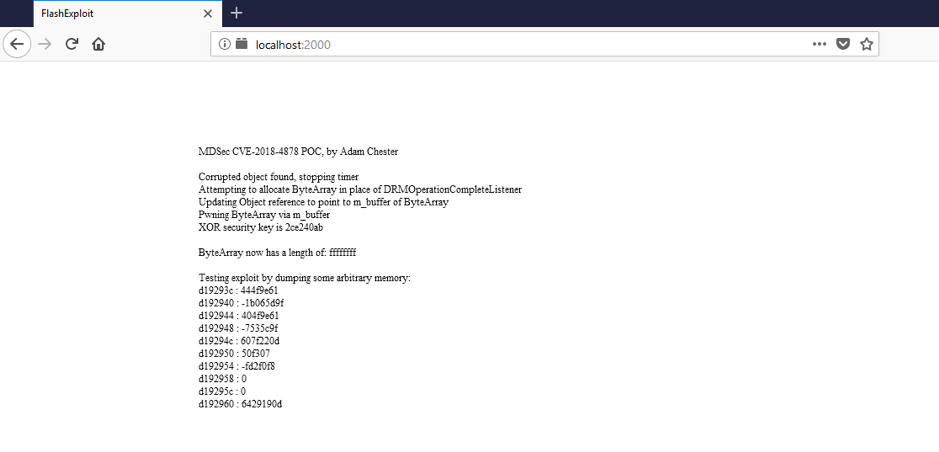
Shortly after joining I was pointed to a small research project, CVE-2018-4878, a Flash vulnerability classified as a “Use-After-Free”.
This vulnerability was being exploited in the wild, however due to the way in which the malware was encrypted, it was not possible to recover a live sample of the exploit. Basing research on some redacted screenshots and snippets disclosed on Twitter, I was able to create a working demo of the exploit.
To see the full blog post, and learn how this vulnerability can be exploited to gain arbitrary R/W over process memory, head over to MDSec’s Blog here.