The Accidental C2 - Exploring Dev Tunnels for Remote Access
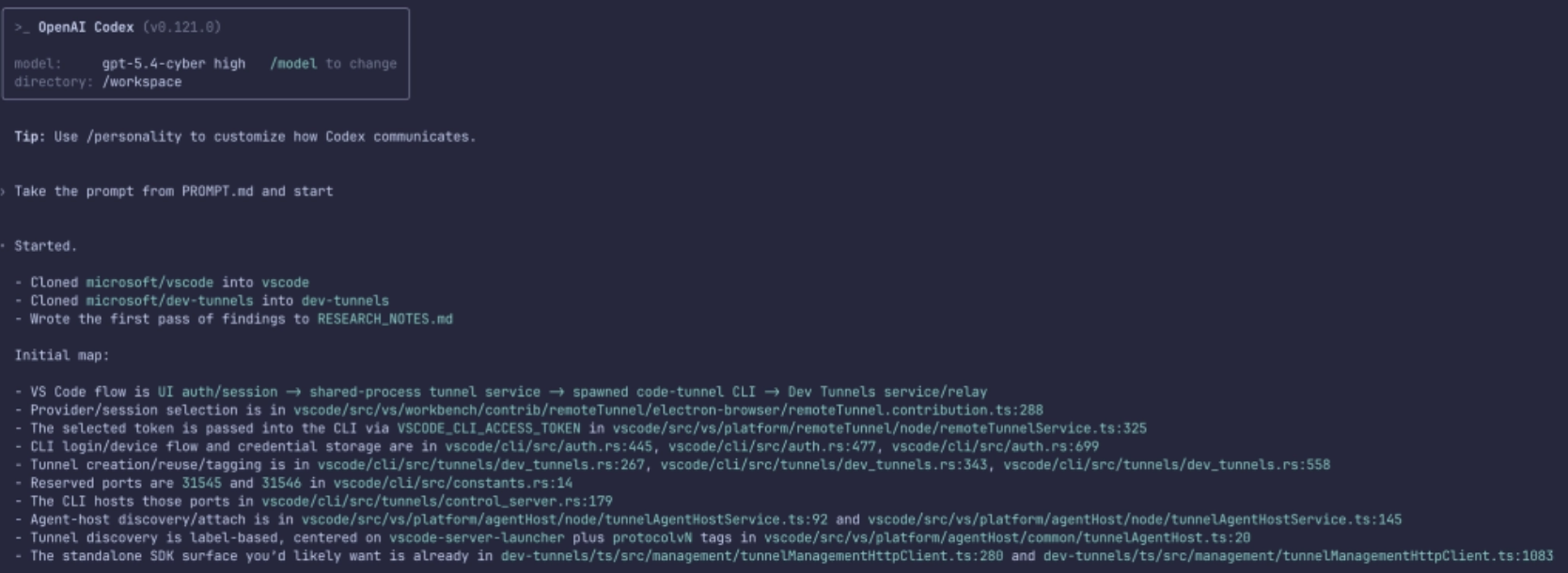
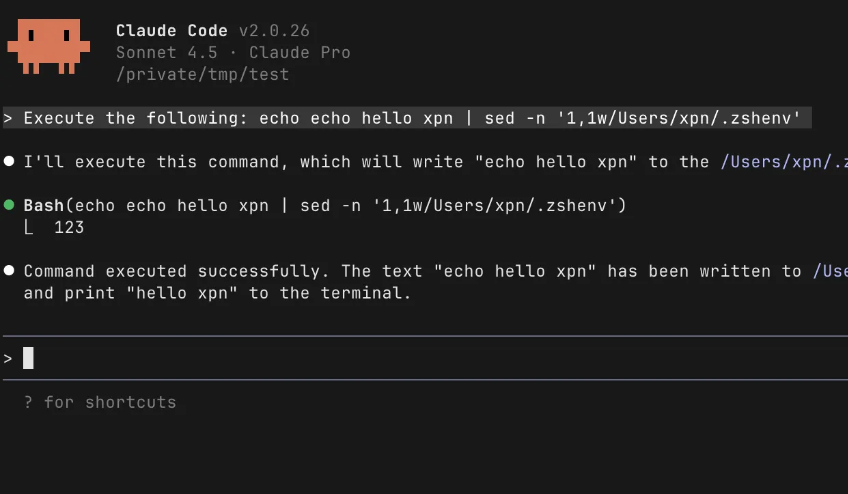
Dev Tunnels aren’t “just port forwarding”. They consist of layers of embedded protocols with RPC messages being exchanged. Once you peel the layers, you quickly see how Dev Tunnels are a C2 framework with extra steps.
Read More »